Why businesses ignore the U.S. government’s information sharing programs
Widespread over-classification of cyber threat intelligence collected by the U.S. government is causing most of the existing information sharing programs between the private and public sector to be less effective, former U.S. officials say.
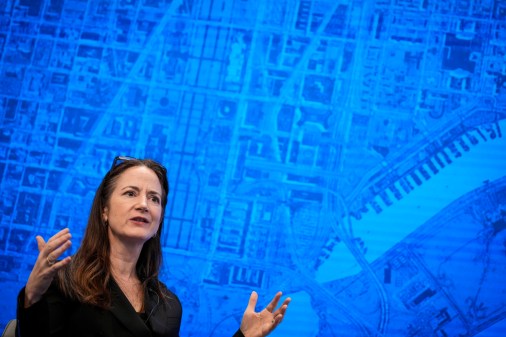
“Over-classification is an issue across the board in the intelligence community in all kinds of different contexts,” Susan Hennessey, a former National Security Agency attorney said during a panel discussion at D.C. think tank New America. “The incentives run here towards keeping information secret. That said, there has been a real effort over the last several years to try to share more information. And this where, I think, we run into an issue of bureaucracy and [culture].”
In late December, the Department of Homeland Security in coordination with the FBI released a technical report, dubbed “Grizzly Steppe,” which contained indicators of compromise associated with the hackers thought to be responsible for the intrusions at the Democratic National Committee. Shortly thereafter, the Office of the Director of Intelligence published another, separate report detailing connections between this hacking group, known as APT28 or Fancy Bear, to high ranking Russian officials.
Cybersecurity experts largely criticized the joint FBI-DHS technical report, describing it as flawed, incomplete and technically inaccurate. The report designated multiple IP addresses as malicious but turned out to link back to harmless domains.
“Grizzly Steppe’s indicator list contains significant errors, lumping in genuine APT28 and APT29 activity with indicators not uniquely related to Russian Government operations,” FireEye Horizons Manager Christopher Porter previously told CyberScoop. “Unfortunately, the inclusion of so many unreviewed and erroneous indicators in the first report … has provided significant ammunition for critics already inclined to be skeptical of the attribution case.”
While the intelligence community must consider both public benefit and operational risks when disclosing confidential information about a threat, agencies have long erred on the side of caution when it comes to cyber incidents, said New Jersey’s Chief Technology Officer Dave Weinstein, and that’s led to a divide.
Bilateral cyber intelligence sharing programs designed by the federal government — like DHS’ Cyber Information Sharing and Collaboration Program — have also seen limited interaction because the private sector can instead turn to private cybersecurity firms, including FireEye, CrowdStrike and Symantec, to acquire advanced intelligence gathering capabilities, explained Robert Lee, a former cyber warfare operations officer with the U.S. Air Force.
This juxtaposition between demand for relevant cyberthreat data and supply from private firms has resulted in a public-private relationship that is largely not conducive to sharing, the panel agreed.
“[The Russian hacking reports] read to me like a document where there was lots and lots of information and they couldn’t come to an agreement regarding what should become public and so they just stripped it all out and gave top line conclusions,” Hennessey described, “the problem is that mismatch between the context, the expectations and the actual information you’re putting forward, that can actually end up undermining confidence.”
“The government is going to find that it is increasingly difficult to get the private sector to share the data to which it needs if it doesn’t put its best foot forward,” said Lee. “I would note that even when I am critical of the … Grizzly Steppe report, I know many of the people, the intelligence analysts that put data into that and they’re fantastic people working incredible mission sets, the bureaucracy is what’s getting in the way,”
Last year, FBI Director James Comey similarly spoke to the larger disconnect that currently exists between law enforcement and U.S. businesses in the aftermath of a data breach.
“All the information, all the evidence we need, sits in private hands in the United States and that is a wonderful thing,” Comey said during a keynote speech at Symantec’s annual government conference. “[But] we have discovered that the majority of our private partners do not turn to law enforcement when they face an intrusion. And that is a very big problem.”
As of December, only two private sector companies and one federal entity were sending cyber threat data through DHS’s Automated Indicator Sharing program, which was originally designed to streamline and encourage the sharing of relevant intelligence. Several additional companies and federal entities are conducting testing with DHS for future sharing, but those commitments remain unclear.