After Dyn cyberattack, lawmakers seek best path forward
More than three weeks after a massive distributed denial of service attack disrupted American websites — downing major properties like Twitter and eBay for several hours — lawmakers took to Capitol Hill Wednesday to explore how the nation should move forward.
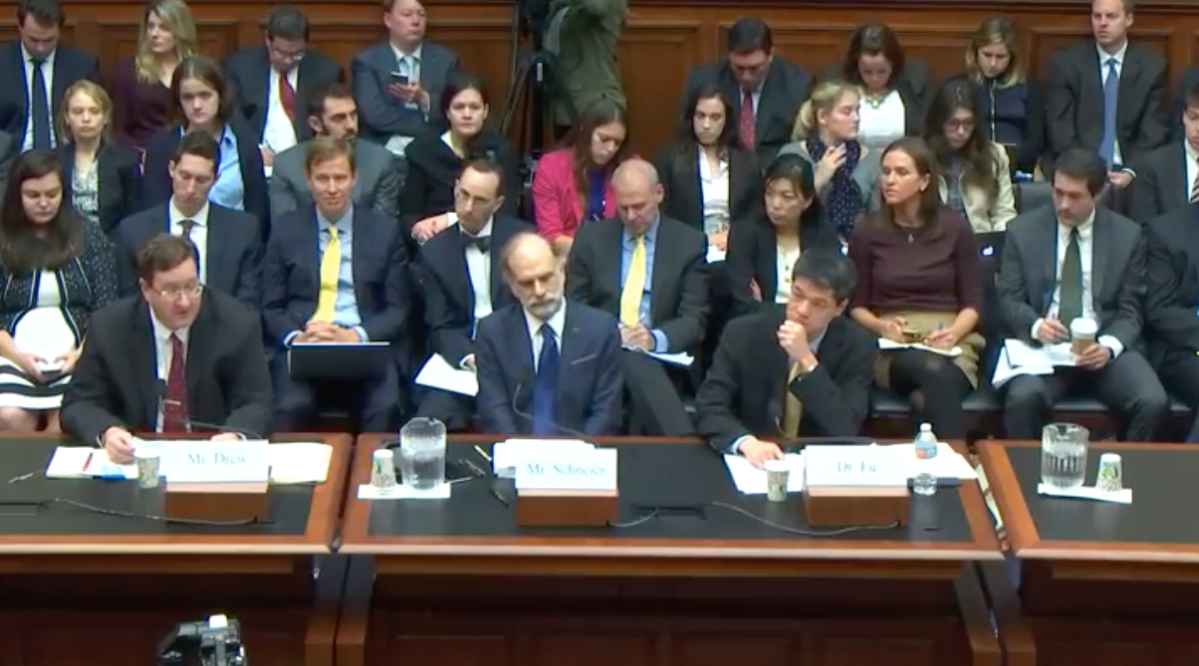
In a hearing hosted by the House Energy and Commerce Committee, University of Michigan professor Kevin Fu, Level 3 Communications’ Chief Security Officer Dale Drew and computer security luminary Bruce Schneier briefed Congress on the challenges posed by insecure internet-connected devices and whether they believe the government can make a difference.
Over the course of a more than two hour hearing, lawmakers shared their genuine confusion, curiosity and unified fear concerning the rise of so-called Internet of Things products; often tossing open-ended questions to the panel on how to best design policy that encourages better security.
“I don’t want my refrigerator talking to some food police,” Rep. Greg Walden, R-Ore., said between a burst of laughter.
At the moment, many consumer electronics makers fail to prioritize cybersecurity because they aren’t realizing a financial benefit or conversely, some form of regulatory punishment, the panel explained.
“The internet empowers attackers,” said Schneier, “it allows attacks to scale. The internet is a massive tool to make things more efficient. And that’s also true for attacking.”
The average citizen isn’t concerned about security for their internet-connected devices so long as a major, catastrophic event doesn’t occur. Security researchers hope that the current Congress will act before such an incident forces a desperate decision from Washington in the future.
On Oct. 21, a renegade group of loosely organized hackers launched a coordinated DDoS attack on internet traffic management company Dyn. By targeting the upstream architecture provider relied upon by numerous businesses to host content online, the hacker effectively manipulated a substantial portion of the internet; causing havoc, confusion and perhaps more importantly, tangible financial losses.
An investigation into the Dyn cyberattack showed that the hackers were leveraging a unique cohort of botnets to launch the DDoS. The botnets contained compromised non-traditional internet connected devices, many of which were made overseas, including security cameras, DVRs and routers.
“The Dyn attack was benign, a couple of websites went down,” Schneier said, “the Internet of Things affects the world in a direct and physical manner: cars, appliances, thermostats, airplanes. There are real risks to life and property.”
Fu recommended that government be more involved in shaping market “incentives” that would, in theory, help guide the behavior of manufacturers as they develop new interconnect hardware. These “incentives” can include, but are not limited to, the introduction of new cybersecurity standards, a regulatory punishment mechanism and a product security rating system.
“There are new vulnerabilities in the interconnections. The more we connect things to each other the more we see vulnerabilities in one thing affect another thing,” said Schneier, “vulnerabilities like this are hard to fix because no one system might be at fault. It could be that two secure things come together and it creates insecurities.”
One of the ideas floated to the House Energy and Commerce Committee was the creation of a new, cybersecurity-focused federal agency that would be solely focused on authoring generic rules, standards and procedure to curb both the creation and use of vulnerable systems across multiple sectors.
“I’d like to see more responsibility put on the manufacturers than there is today. But I [would] provide that incentive to them [as well],” said Drew, “So I am going back to standards, I am going back to certifications and stands, you see that seal of approval on a device and then you know that the device is more protected than others.”



