Supermicro concludes ‘Big Hack’ investigation, says no tampering

Executives at Super Micro Computer (Supermicro) contended Tuesday that their company did not fall victim to a major supply chain compromise described in a Bloomberg Businessweek story in October.
CEO Charles Liang and senior vice presidents David Weigand and Raju Penumatcha wrote in a letter to customers that a “thorough investigation” by a third-party firm concluded that malicious hardware had not been planted on Supermicro devices.
“Recent reports in the media wrongly alleged that bad actors had inserted a malicious chip or other hardware on our products during our manufacturing process,” the letter reads. “After thorough examination and a range of functional tests, the investigations firm found absolutely no evidence of malicious hardware on our motherboards.”
The Bloomberg story alleged Chinese operatives embedded rice grain-sized chips on motherboards that Supermicro supplied to major technology companies like Apple and Amazon Web Services. The report was immediately met with strong denials from Supermicro and other organizations implicated. Public officials like lawmakers, the FBI director, the director of national intelligence and others also scrutinized the Bloomberg story.
“As we have stated repeatedly since these allegations were reported, no government agency has ever informed us that it has found malicious hardware on our products; no customer has ever informed us that it found malicious hardware on our products; and we have never seen any evidence of malicious hardware on our products,” Supermicro wrote.
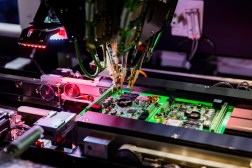
The San Jose, California, company said its investigation looked into the manufacturing, auditing, oversight and testing aspects of its production process and could not corroborate the Bloomberg report. The company noted that Supermicro employees are always present with subcontractors (a potential source of compromise), that subcontractors are vetted and that boards are routinely examined by X-rays and other methods for irregularities.
At a Wall Street Journal event in New York City on Tuesday, a senior U.S. government official added to the chorus casting doubt on a reported major supply chain attack, although without explicitly mentioning Supermicro.
“I’ve still seen no examples of hardware tampering, or seen examples of that from anyone else,” said Rob Joyce, a senior adviser for cybersecurity strategy at the National Security Agency.
Joyce noted that from a hacker’s perspective, hardware is one of the most difficult things for an adversary to actually compromise, compared with things like software and personnel.
“There’s certainly a hierarchy of supply chain. When you think about securing your businesses and networks you should be thinking down the pyramid. You need to think about the people you need to give your keys to the business kingdom. Next layer down is the software and services you use,” Joyce said. “You’ve got to worry about the people you intentionally let in first. Hardware is way down the list. It’s really hard to do, its expensive. It leaves a physical trail.”
Alongside its letter, Supermicro released a highly produced video defending its production and oversight process.
“We check every board. We check every layer of every board. And then, we check again,” the video says.
Jeff Stone contributed to this story.