Software vulnerabilities used to spread WannaCry are favorites for hackers, FireEye says

The same Microsoft Windows’ software vulnerabilities that allowed the WannaCry ransomware to spread globally are now being used by a wide array of hackers to infect computers with remote access trojans, according to new research by U.S. cybersecurity firm FireEye.
The research serves to show just how widespread the use of “EternalBlue,” otherwise known as the MS017-010 exploit, continues to be. Although Microsoft previously issued several different software security updates for older versions of Windows, many computers remain unpatched and therefore vulnerable.
The addition of the EternalBlue exploit to Metasploit, software made for penetration testing but which is also used for illegal hacking, “has made it easy for threat actors to exploit these vulnerabilities,” a FireEye blog post reads.
“In the coming weeks and months, we expect to see more attackers leveraging these vulnerabilities and to spread such infections with different payloads,” the post says.
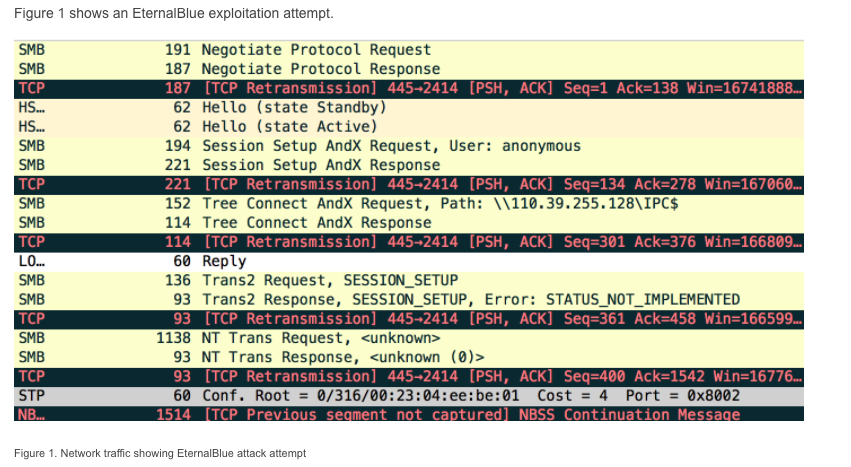
Image via FireEye
According to FireEye researchers, well-known malware payloads like “Backdoor.Nitol,” which have been typically loaded onto victim computers using other exploits, are being increasingly combined with EternalBlue instead. Backdoor.Nitol is a stealthy implant that is used in targeted attacks.
“In the latest attacks that we have seen with non-WannaCry payloads, we didn’t observe a worm-able component yet which means less noise,” Ali Islam Khan, FireEye’s director of research and development, told CyberScoop. “One can assume that noise was removed to prepare it for a more stealthy and targeted kind of attack.”
FireEye found in one case that EternalBlue was used in tandem with VBScript, a Microsoft active scripting language, to first compromise and then fetch malware from another server. This technique was used to “distribute Gh0st RAT in Singapore, as well as Backdoor.Nitol being delivered in the South Asia region.”
Gh0st Rat is a remote access trojan, or RAT, that has been used in the past by hackers to compromise businesses involved in the education, energy, utilities, manufacturing, consulting and telecom industries. There are various different variants of Gh0st Rat, with the original virus first appearing around 2001. As a tool, Gh0St Rat provides hackers with significant espionage capabilities, including keystroke logging, camera and microphone access.
The use of EternalBlue to spread Gh0st Rat is just one of multiple new cases being studied by security researchers.
“Just after releasing the blog we saw another attack … with a different payload which looked like a RAT different from Nitol and Gh0stRat,” Khan said. “We are still researching the new RAT and might update our blog after the investigation.”
He added, “there is definitely a trend of frequent use of EternalBlue.”
EternalBlue effectively leverages two different coding flaws in older versions of Microsoft Windows to propagate malware on a targeted computer network. In practice, this exploit breaks a network file-sharing protocol known as the server message block, or SMB. Operating systems vulnerable to EternalBlue include Windows XP, Windows Vista SP2, Windows 7, Windows Server 2008 R2 and Windows Server 2012 — each remains popularly used, especially outside of the U.S.
“The frequent use of SMB exploits can be game changer and can force the security companies to adjust their defense mechanisms. And remember there are other potential SMB vulnerabilities in future which can be part of regular dumps,” said Khan.
Experts believe that the high-quality exploit will be used in the coming years by both amateurish hackers and sophisticated threat actors to steal information.
EternalBlue first became publicly accessible after the full operational computer code for the tool was posted online, as part of a leaked National Security Agency document, published by a mysterious group named the Shadow Brokers.
“We believe there is still a large number of unpatched machines out on internet which attackers can target and exploit,” Khan said.


