New vuln discovered in Schneider Electric software, patches already issued
A significant vulnerability in Schneider Electric software used at manufacturing and energy facilities could allow hackers to execute arbitrary code and, “in a worst-case scenario, disrupt or cripple plant operations,” cybersecurity firm Tenable announced Wednesday.
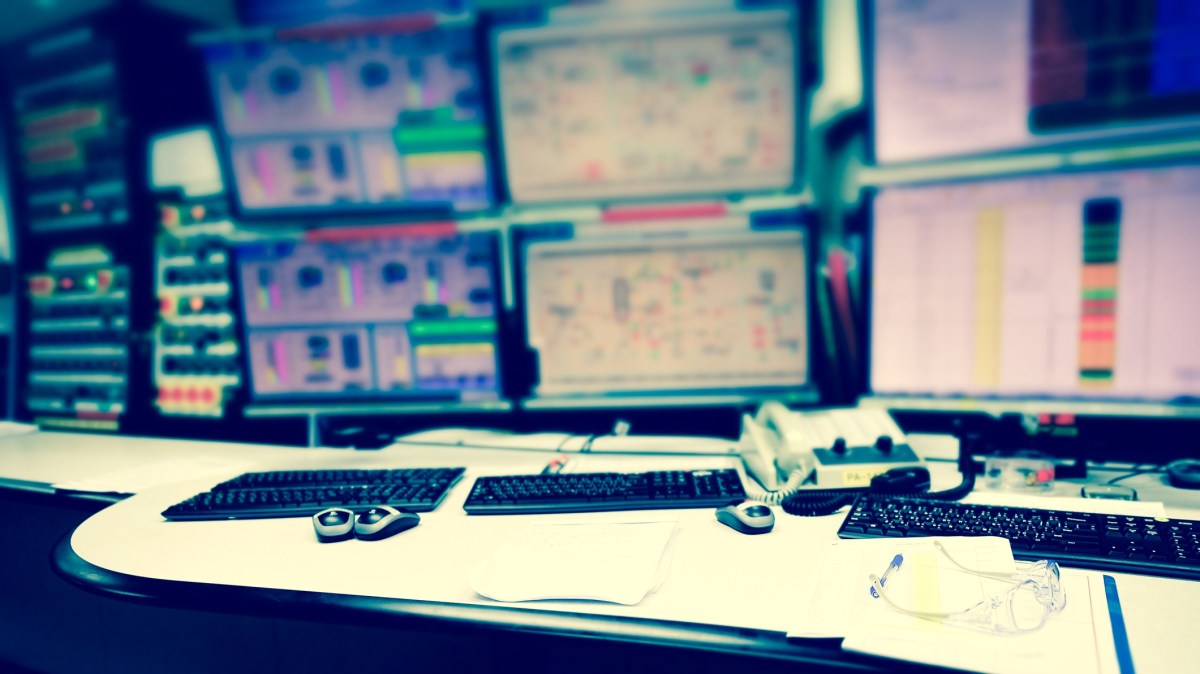
According to the Maryland-based company, an attacker without credentials could use the vulnerability to compromise Schneider Electric software used to develop – and build applications for – the human machine interfaces (HMIs) and supervisory control and data acquisition (SCADA) systems that drive industrial automation. After compromising a machine, a hacker could move laterally within an organization’s network to carry out other attacks, according to Tenable.
Schneider Electric issued patches for the software – versions of InduSoft Web Studio and InTouch Machine Edition – and urged affected customers to swiftly apply them lest an attacker use the vulnerability to “remotely execute code with high privileges.”
“This Schneider Electric vulnerability is particularly concerning because of the potential access it grants cybercriminals looking to do serious damage to mission-critical systems that quite literally power our communities,” Dave Cole, Tenable’s chief product officer, said in a statement that praised Schneider Electric for quickly releasing a patch.
Tenable cast the new vulnerability as another chink in the armor of an increasingly digital infrastructure.
“With the growing adoption of distributed and remote monitoring in industrial environments, [operational technology] and IT are converging,” Columbia, Md.-based Tenable said.
The increasing connectivity of OT systems opens up new vulnerabilities to hacking, the firm added.
Software that supports industrial control systems has been in the security limelight in recent months.
Last August, hackers targeted Schneider Electric’s Triconex safety system software in a rare and sophisticated ICS-tailored attack, causing an unidentified energy plant to shut down. CyberScoop reported that the affected facility was an oil and gas plant in Saudi Arabia, and that the attackers’ malware, dubbed Triton or Trisis, had been stumping security experts.
Schneider Electric won plaudits for its transparency from cybersecurity experts after the energy software giant presented lessons learned from the incident at a popular conference.
Public disclosure of the new HMI/SCADA software vulnerability comes weeks after U.S. officials warned that Russian government hackers were targeting the U.S. energy and manufacturing sectors, among others, in a two-year, multi-stage campaign.



