NeverQuest banking malware administrator sentenced to 4 years

A Russian man who helped create a hacking tool capable of extracting funds from victims’ bank accounts will spend four years behind bars, a punishment that fell short of the five years for which federal prosecutors had asked.
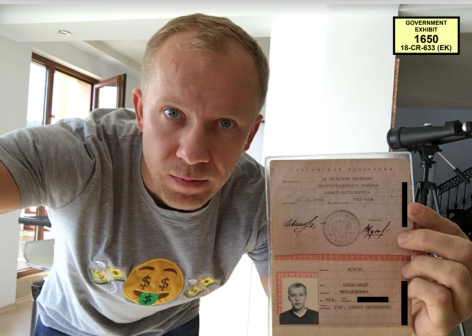
A judge in the U.S. Southern District of New York handed down the 48-month prison sentence, including time served, to Stanislav Lisov for his role in deploying the NeverQuest malware. Lisov admitted he profited $885,000 from NeverQuest, while government investigators said the hacking technique had been used to try to steal a total of $4.4 million from international banks.
Five years would have been the maximum allowed under the terms of a plea deal Lisov struck with the Department of Justice early this year.
“He is happy,” Lisov’s attorney, Arkady Bukh, told CyberScoop, calling the sentence a “great victory.”
NeverQuest quickly became a favorite hacking tool for financial scammers after its debut in 2013. Thieves would infect victims via social media, phishing emails or file transfers, wait for them to access a banking site, and then capture the credentials. Hackers also maintained a database of financial websites, allowing them to automatically capture any data a victim entered into their bank’s site.
“Once surreptitiously installed, NeverQuest enables its administrators remotely to control a victim’s computer and log into the victim’s online banking or financial accounts, transfer money to other accounts, change login credentials, write online checks, and purchase goods from online vendors,” the Department of Justice said in a court filing.
Lisov played a central role in creating this malware. Between 2012 and 2015, he controlled the network of victims’ hacked computers, called a botnet, oversaw the computer servers for that botnet and was in possession of approximately 1.7 million stolen usernames and passwords.
Meanwhile he also used the NeverQuest malware himself and verified that co-conspirators were using the tool properly. In one conversation reproduced by prosecutors, Lisov tells an unnamed associate they successfully breached 400 Citi accounts, all with balances of more than $1,000.
He was initially arrested by Spanish authorities in January 2017 and extradited to the U.S. in 2018. He pleaded guilty in February.
The government’s sentencing request is available in full below.
[documentcloud url=”http://www.documentcloud.org/documents/6555752-Lisov.html” responsive=true]