DHS memo: ‘Significant’ security risks presented by online voting

The Department of Homeland Security has told election officials and voting vendors that internet-connected voting is risky to the point that ballots returned online “could be manipulated at scale” by a malicious attacker.
The advisory that DHS’s Cybersecurity and Infrastructure Security Agency sent states on Friday is perhaps the federal government’s sternest warning yet against online voting. It comes as officials weigh their options for conducting elections during a pandemic and as digital voting vendors see an opportunity to hawk their products.
While the risk of election officials delivering ballots to voters via the internet can be managed, the return of those ballots by voters “faces significant security risks to the confidentiality, integrity, and availability of voted ballots,” CISA said in the guidance, which CyberScoop reviewed. “These risks can ultimately affect the tabulation and results and, can occur at scale.”
The guidance, which is marked “For Official Use Only” and is not public, cites a theoretical “man-in-the-middle” attack, in which a hacker intercepts and alters data, as one risk to voters who return ballots electronically. Other federal agencies involved in election security — the Election Assistance Commission, the FBI, and the National Institute of Standards and Technology — signed off on the document.
“[W]e recommend paper ballot returns as electronic ballot return technologies are high-risk even with controls in place,” the agencies said in a joint public statement. “Election officials are best positioned to evaluate the risks and make decisions accordingly.”
It’s the latest step by federal officials to make voting infrastructure more secure since the 2016 election, when Russian hackers probed state IT systems and managed to breach Illinois’s voter registration database. There is no evidence that votes were changed, and voting machines themselves weren’t compromised.
In a given general election, the number of ballots received via the internet — often from overseas or military voters — is a fraction of the votes cast. Instead, most votes are cast via paper ballots. Out of the 140 million votes cast in the 2016 presidential election, at least 100,000 ballots were returned via the internet, according to a 2018 report from governance watchdog Common Cause and others. (Not all states reported data in that survey, meaning the number of ballots sent via the internet was likely much higher, according to the report.)
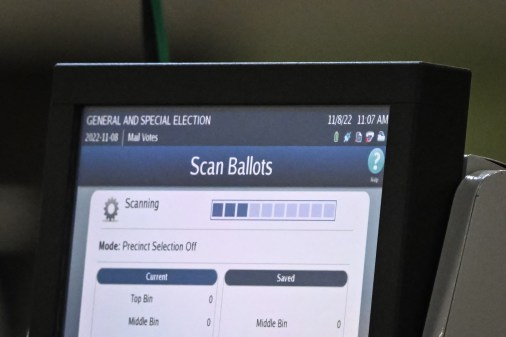
The quest to secure voting infrastructure with internet connectivity goes beyond ballot returns. Researchers last year found over 30 election-management systems, used to receive encrypted vote totals, behind internet-accessible firewalls. The country’s top voting vendors say they have robust cybersecurity testing in place for such systems.
While clear in outlining the risk, the final CISA guidance wasn’t as forceful in criticizing online voting in one passage as a draft version was. A line from the draft document stating that CISA “discourages electronic ballot return technologies” was removed out of concern it could expose the federal government to lawsuits from voting technology vendors, according to a person familiar with the document.
The Wall Street Journal was first to report on the final version of the guidance. The Guardian reported on a draft version on Friday.
Mobile voting takes another hit
The assessment is a blow to mobile voting platforms that have tried to make inroads in a market dominated by traditional voting-machine manufacturers. Cybersecurity experts have warned that mobile platforms like one offered by Voatz, a Massachusetts-based company, could be exploited by hackers. Ramping up voting-by-mail options, they say, would be a more secure response to COVID-19, which has forced several states to cancel or postpone their primaries.
Voatz, whose software has been used by a handful of U.S. counties in elections in the last year, has continued to market its technology as an alternative to voting by mail amid the coronavirus pandemic. The company says it uses a matching paper record for vote verification.
“We are in alignment with our federal agencies that we must work to ensure the highest standards of security in the voting options available” to voters who cast their ballots electronically, a Voatz spokesperson said in response to the CISA report.
In a statement, West Virginia Secretary of State Mac Warner said his state “is not using online voting as a solution for COVID-19 threats.” West Virginia reportedly had plans to allow voters with disabilities to use Voatz’s smartphone app in the state’s presidential primary before an MIT report found numerous vulnerabilities in the software. West Virginia is now offering voters with disabilities the option of voting via another mobile platform, made by Democracy Live.
“Online voting in West Virginia is only available for those that otherwise would be disenfranchised due to all other options, including election day polling locations not being available,” Warner said.
Election security advocates welcomed the new CISA guidance.
“As election officials consider how best to conduct safe, secure elections during the coronavirus pandemic, it is understandable that some are exploring internet voting options,” said David Levine, an elections integrity fellow at the German Marshall Fund of the United States’ Alliance for Securing Democracy. “However, as this guidance is the latest to point out, internet voting is still not ready or secure enough for primetime.”
In a recent study, Levine and other election security analysts found that the $400 million Congress allotted in March to help states run elections during the pandemic is only a fraction of what is needed to increase voting by mail, provide protective gear to election workers, and educate the public. The money, for example, will only cover a tenth of what officials in Georgia need.
Rep. Jim Langevin, D-R.I., a member of the House Homeland Security Committee, urged CISA “to make the guidance public so that voters around the country have a better understanding of what is at risk.”
“Our intelligence community has warned that malicious state actors such as Russia are trying to interfere in our elections, and we must heed the recommendations of the experts at CISA to bolster our systems,” Langevin said in a statement.
UPDATE, 4:18 p.m. EDT: This story has been updated with a statement from Voatz.