- Sponsored
- Technology
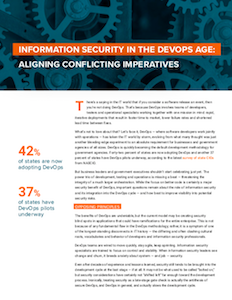
Information security in the DevOps age: Aligning conflicting imperatives

DevOps is quickly becoming the default development methodology for government agencies. Forty-two percent of states are now adopting DevOps and another 37 percent of states have DevOps pilots underway, according to the latest survey of state CIOs from the National Association of State Chief Information Officers.
The benefits of DevOps are undeniable, but the current model may be creating security blind spots in applications that could have ramifications for the entire enterprise.
Download the full report.
A new CyberScoop special report, underwritten by Tenable, explores how organizations can narrow the collaboration gaps between developers and information security professionals that can lead to costly enterprise security vulnerabilities. It also explains how a new generation of automated tests can quickly identify coding vulnerabilities in ways that jointly support the needs of DevOps and information security teams.
The report delves into the increasing importance of software containers for DevOps team. Containers speed application development and deployment by providing developers self-contained packages that have everything necessary to run an application: the application, dependencies, libraries, binaries and configuration files.
The adoption of container technologies has exploded in recent years. In the case of Docker— the leading open source container technology for the past three years — adoption has grown 40 percent year over year, according to recent Datadog user data. Docker offers more than 500,000 apps in its community registry.
But containers present special security inspection challenges. Scheduling traditional vulnerability scans, for instance, requires multiple credentials used by privileged users. They can also tax network resources. And remediating vulnerabilities becomes more difficult without full visibility into containers.
One key way for security leaders to work with DevOps is to integrate vulnerability remediation into the Continuous Integration and Continuous Deployment (CI/CD) tool chain. CI is focused on building the application — the development process — and CD is focused on deployment after testing.
Automated tests, using products such as Tenable.io Container Security, allow IT security teams to quickly identify coding vulnerabilities in less than 30 seconds during each new software build. Moreover, IT security professionals are now able to protect containers from newly identified threats, using Tenable.io Container Security to monitor a wide range of external vulnerability databases.
Download the special report, “Information security in the DevOps age: Aligning conflicting imperatives” for more on ways to bridge the divide between DevOps and infosec teams, using shared intelligence, language and purpose to improve speed to fulfillment and security.
This article was produced by CyberScoop and sponsored by Tenable.



