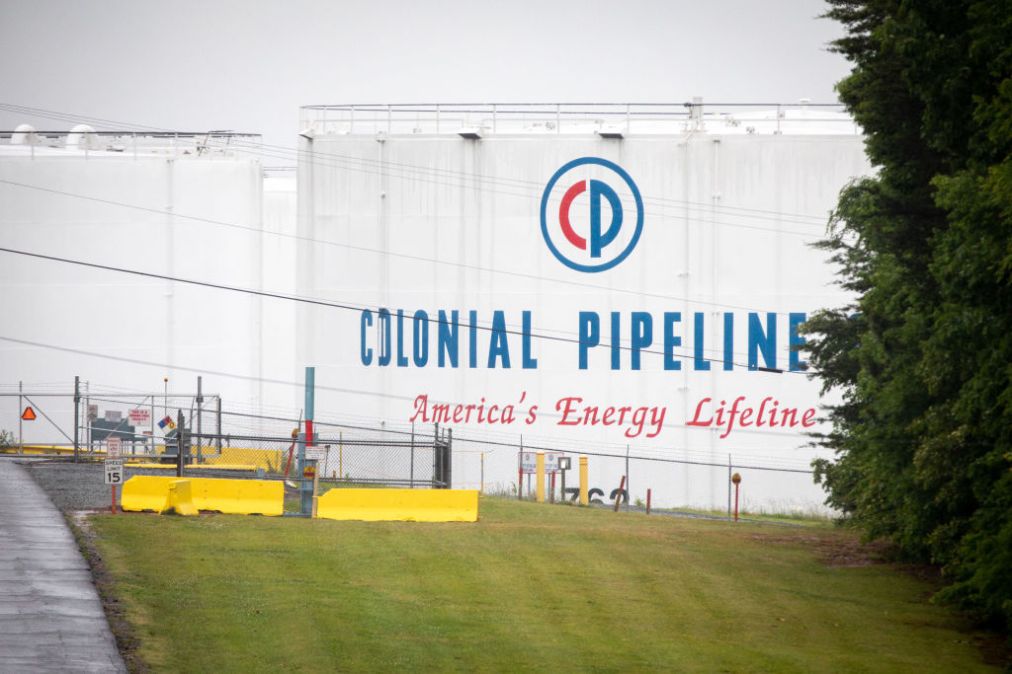
Colonial Pipeline CEO to face questions from Congress on $4.4 million ransom payment
After Colonial Pipeline CEO Joseph Blount confirmed Wednesday that his company had paid hackers $4.4 million to recover its data, lawmakers said they would press Blount for more information at a congressional hearing next month.
“I’ll have some questions about Blount’s judgement when he appears before [the committee] in a couple weeks,” tweeted Rep. Jim Langevin, D-R.I., an influential member of the House Homeland Security Committee.
The FBI has advised companies for years not to pay a ransom, and cybersecurity experts warn that doing so fuels yet more ransomware hacks that have already cost U.S. companies hundreds of millions of dollars.But the breach of Colonial Pipeline’s IT systems, which caused a multi-day shutdown of the pipeline system and indirectly resulted in shortages at gas stations in multiple states, has thrust the issue of ransomware payments into the national limelight.
Blount defended the decision in an interview with The Wall Street Journal, saying he authorized the payment because he didn’t know how long it would take to restore service for the pipeline, which provides more than 100 million gallons of fuel daily to customers from Texas to New York.
“It was the right thing to do for the country,” Blount said.
Rep. Langevin disagreed.
“Paying cyber criminals $4.4 million, while freezing out the FBI and [the Cybersecurity and Infrastructure Security Agency] is not ‘good for the country,’” the normally mild-mannered Rhode Island Democrat tweeted Wednesday. He was referring to reports of a lack of clear communication between Colonial Pipeline and federal agencies regarding the ransomware attack.
Colonial Pipeline has said it has worked closely with federal investigators. Blount said that Colonial executives called FBI offices and a CISA representative to notify them of the incident.
“It is deeply disappointing that Colonial Pipeline still has not answered questions from Congress about its multi-million dollar ransomware payments to cybercriminal groups in Eastern Europe, despite discussing these payments in the press,” Rep. Carolyn Maloney, D-N.Y., the chairwoman of the House Oversight and Reform Committee, told CyberScoop.
“The company’s CEO said his decision to pay the ransom ‘was the right thing to do for the country,’’’ Maloney added. “But rather than make this problem go away, Colonial’s hasty decision sets a dangerous precedent and puts an even bigger target on the back of critical infrastructure by showing that criminals can extort companies into paying millions of dollars in the desperate hopes of quickly restoring services.”
Some analysts sympathized with Colonial Pipeline’s decision to pay the hackers — one that countless other companies have made under pressure to bring their businesses back online.
“With the whole world looking at you, what’s the other option?” said Tatyana Bolton, a former Department of Homeland Security official who is now director of cybersecurity and emerging threats at the nonprofit R Street Institute.
Everyone from President Joe Biden to Colonial Pipeline executives had for days declined to comment on any ransom paid to the hackers, whom the FBI has linked to the DarkSide, a Russian-speaking crime syndicate.
The dearth of information irked lawmakers. Following a Monday briefing with Colonial Pipeline executives, Maloney and Rep. Bennie Thompson, D-Miss., chair of the House Homeland Security Committee, said the company’s refusal to share information on any ransom payment hindered their ability to craft legislation to address the ransomware problem.
A spokesperson for House Homeland Security Ranking Member John Katko, R-N.Y., said Wednesday that the congressman agreed that more information from Colonial Pipeline on the ransom payment would help with a legislative response to ransomware incidents.
Colonial Pipeline’s cybersecurity practices have also come under scrutiny in the wake of the hack.
“The question should not be whether or not Colonial Pipeline should have paid the ransom, but why, as the company responsible for 45% of gas and jet fuel to the East Coast, were they even in this position in the first place,” said Kiersten Todt, managing director of the Cyber Readiness Institute.
“[I]f the ability of carrying gas to the East Coast was in question, they absolutely should have reached out to the federal government for help immediately — rather than try to cover up their weakness,” Todt said.
Colonial Pipeline has defended its cybersecurity practices.
Blount told The Journal that Colonial has spent $200 million on IT issues in the last five years, some of which includes cybersecurity. The company also says that the team supporting its chief information officer has doubled in size over the last four years, and it has “a longer-term growth strategy around cybersecurity talent.”



