Biden administration mulls software security grades after SolarWinds
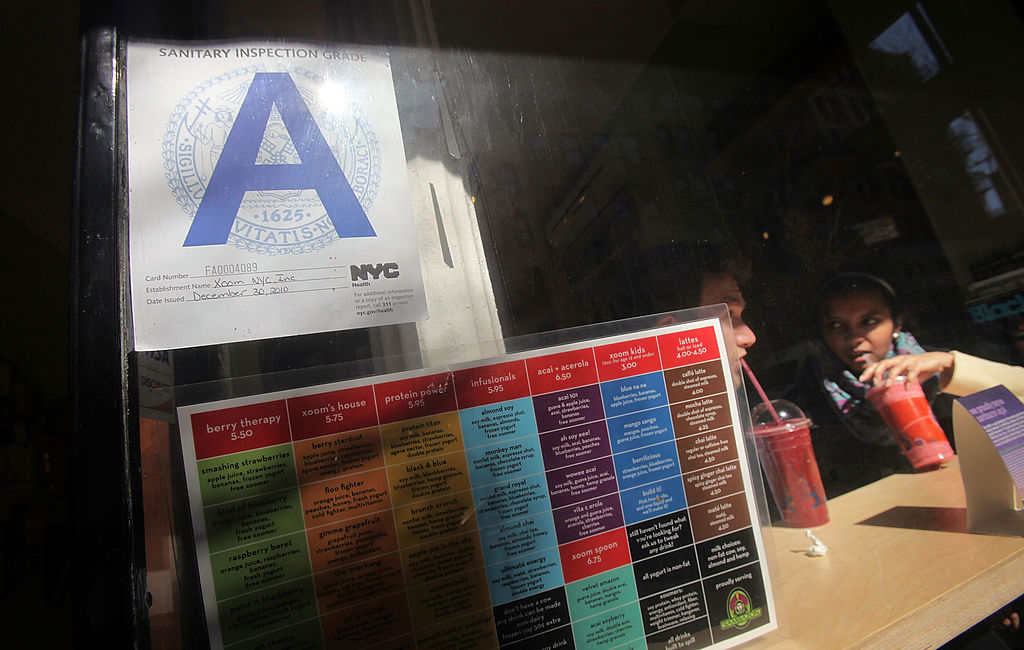
The White House is contemplating the use of cybersecurity ratings and standards for U.S. software, a move akin to how New York City grades restaurants on sanitation or Singapore labels internet of things devices, a senior administration official told reporters on Friday.
“There will be ideas coming on both of those in an executive action in the next few weeks,” the official said, briefing reporters on the condition of anonymity about simultaneous major security incidents that continue to roil the country: the SolarWinds supply chain attack, and the exploitation of Microsoft Exchange Server vulnerabilities.
The concept of government labeling and grading in cybersecurity isn’t entirely new. Some experts have long coveted an Energy Star-style rating system resembling the program that the Environmental Protection Agency and Energy Department use to promote energy-efficient devices. Among them: the Cybersecurity Solarium Commission, which last year recommended that Congress establish a National Cybersecurity Certification and Labeling Authority.
That Solarium proposal is for voluntary labeling, as are Energy Star and the Singapore IoT labeling initiative. If the idea is to mimic the New York City restaurant grades, though, that initiative was mandatory and implementation ran into stiff industry opposition, and the official observed that nothing was improving before Mayor Michael Bloomberg forced restaurants to include a grade card in their windows.
Today, some cost of technology “is born at the end by incident response and clean-up, and we really believe it will cost us less if we build it right at the outset,” the official said.
In the U.S., compared to the Singapore labeling initiative, “we don’t have that transparency so that people can ‘make a market’ for cybersecurity,” according to the official.
Status update for SolarWinds, Microsoft Exchange Server
Most of the agencies compromised in the SolarWinds hack have completed White House-directed fixes and subsequent independent reviews to ensure the attackers were out of their systems, and the remainder are on track to do so by the end of March, the official said.
Soon, the Biden administration will begin rolling out “best of breed commercial” technologies meant to modernize federal agencies with a focus on the nine agencies compromised in the SolarWinds breach, the official said.
The administration has held regular meetings on both SolarWinds and Microsoft Exchange Server, the official said, with President Joe Biden briefed this week on the Microsoft incident. The emergency Cyber Unified Coordination Group (UCG) convened to respond to the Microsoft hacking has, for the first time, invited private sector companies to participate in its meetings, the official said.
The administration convened a separate UCG in December to respond to the SolarWinds incident.
One thing the official said the administration is not doing, however, is seeking additional authorities “at this time” to monitor domestic systems, viewing that as the responsibility of private companies.
And the official said that it would be “weeks, not months” before the administration responds to the SolarWinds hack — a line administration officials have used publicly for nearly three weeks already.
Clarification, 3/17/2021: The story has been clarified to detail there are two UCGs ongoing.



