Scammers promise video proof of fake Clinton scandal, victims get malware instead

A uniquely strange email phishing campaign is finding success by convincing people to click a link that promises a non-existent video, purportedly showing democratic presidential nominee Hillary Clinton exchanging money with terrorists, according to Symantec’s security research team.
When the supposed video download link is clicked, malware is instead installed onto the victim’s computer.
The subject line for the phishing email carries an attention-grabbing, clickbait-focused title: “Clinton Deal ISIS Leader caught on Video.”
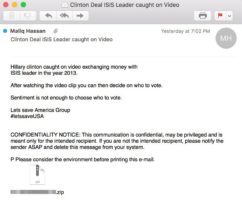
Example of emailing phishing prompt via Symantec research
Research indicates that the email scam has largely targeted American voters — with 85 percent of recipient IP addresses based in the U.S. The body of the email message asks victims to “decide on who to vote [for]” only after they watch the provided video clip.
The fake-attachment will download a Java-based remote access trojan that will automatically analyzes a victim computer’s antivirus and firewall software. The malware then attempts to connect to the device’s command and control server, used in this instance to download and execute additional malicious files. Windows, Mac OS X, Linux and Android operating systems are all susceptible to the cyber attack.
“As with most major events, the U.S. election serves as valuable bait for malicious spam activity. With less than 90 days to go until Election Day, we advise everyone to keep an eye out for suspicious emails that may use either presidential candidate, Hillary Clinton or Donald Trump, as bait,” Symantec Senior Security Response Manager Satnam Narang writes in a blog post.