Rep. Langevin: We need a DHS briefing to understand extent of DNS hijacking threat
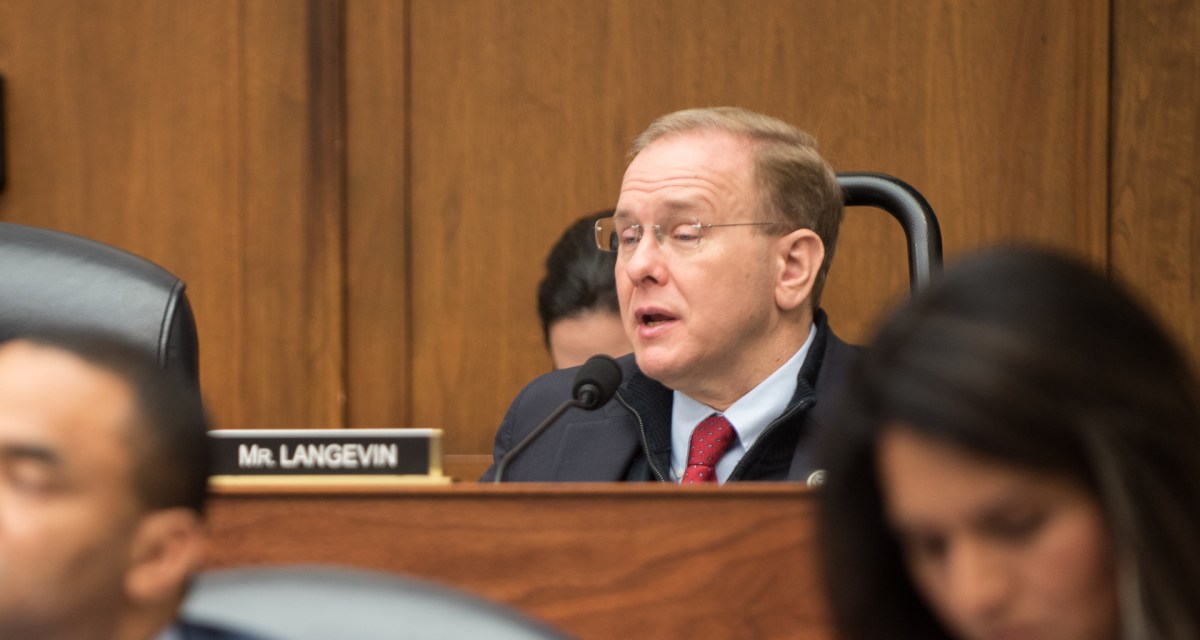
A key House Democrat wants the Department of Homeland Security to brief lawmakers “as soon as possible” on a new domain name system hacking threat to federal computer networks, and the emergency order the department issued in response.
DHS should brief members of the House Homeland Security Committee on the cyberthreat because “we need to understand the scope of this action and how many agencies were actually affected,” Rep. Jim Langevin, D-R.I., said in an interview Wednesday.
Langevin was reacting to a rare emergency directive that DHS issued Tuesday ordering civilian agencies to tighten security controls in the face of a suspected Iranian hacking campaign.
DHS issued the order out of concern that civilian agencies could be vulnerable to cyberattacks on platforms for managing domain name system (DNS) records, which help ensure that a computer user reaches an intended website. By manipulating DNS records, hackers could direct unwitting users to malicious websites. At least six civilian agencies have been affected by the recent malicious DNS activity, people familiar with the matter told CyberScoop.
“It’s a serious issue and obviously any efforts to tamper with the domain name system are very disturbing,” Langevin told CyberScoop. This is the first time DHS has issued an emergency order under a 2015 law granting the department that authority, he added.
“The ability of a malicious actor to redirect traffic is an avenue for…undermining confidence in the dot-gov system, and it can also be used as a conduit for advanced malware,” said Langevin, who credited DHS for issuing the emergency order.
The order gave agencies 10 business days to implement two-factor authentication and change passwords for accounts managing DNS records, among other updates. Langevin also said he worried the ongoing partial government shutdown would hinder agencies’ ability to carry out the directive.
“It’s far from clear who’s actually going to be on hand [at agencies] to implement these changes within the next 10 days,” the Rhode Island Democrat said. “And this needed to be done yesterday, not 10 days from now.”
In a series of tweets Wednesday evening, Chris Krebs, the senior DHS official who issued the emergency directive, explained the importance of mitigating the DNS threat and said the order was implementable, despite the partial government shutdown.
“Though we recognize that some agencies may have challenges implementing the directive during the ongoing partial government shutdown, we believe these actions are necessary, urgent, and implementable as most agencies are adequately staffed to take the necessary actions,” Krebs wrote.
Langevin, who was recently named chairman of the House Armed Services Committee panel that oversees cyber operations, also reflected on a longstanding challenge for policymakers: How do you deter foreign adversaries from laying siege to U.S computer networks?
Langevin said deterrence required a “whole-of-government approach,” including policy options like offensive operations, indictments, and sanctions. The congressman welcomed the “forward-leaning” approach advanced in the Pentagon’s latest cybersecurity strategy, which calls for “halt[ing] malicious cyber activity at its source.”
“I support [that approach], but with proper oversight and appropriate constraints,” Langevin said. “I don’t want this to be a furthering of the Wild West in cyberspace, but done the right way and within reason.”
UPDATE, 1/24, 8:10 a.m. EDT: This story has been updated with a statement from Chris Krebs, director of DHS’s Cybersecurity and Infrastructure Security Agency.



