Pacemaker updates seal vulnerabilities affecting nearly a half-million U.S. patients
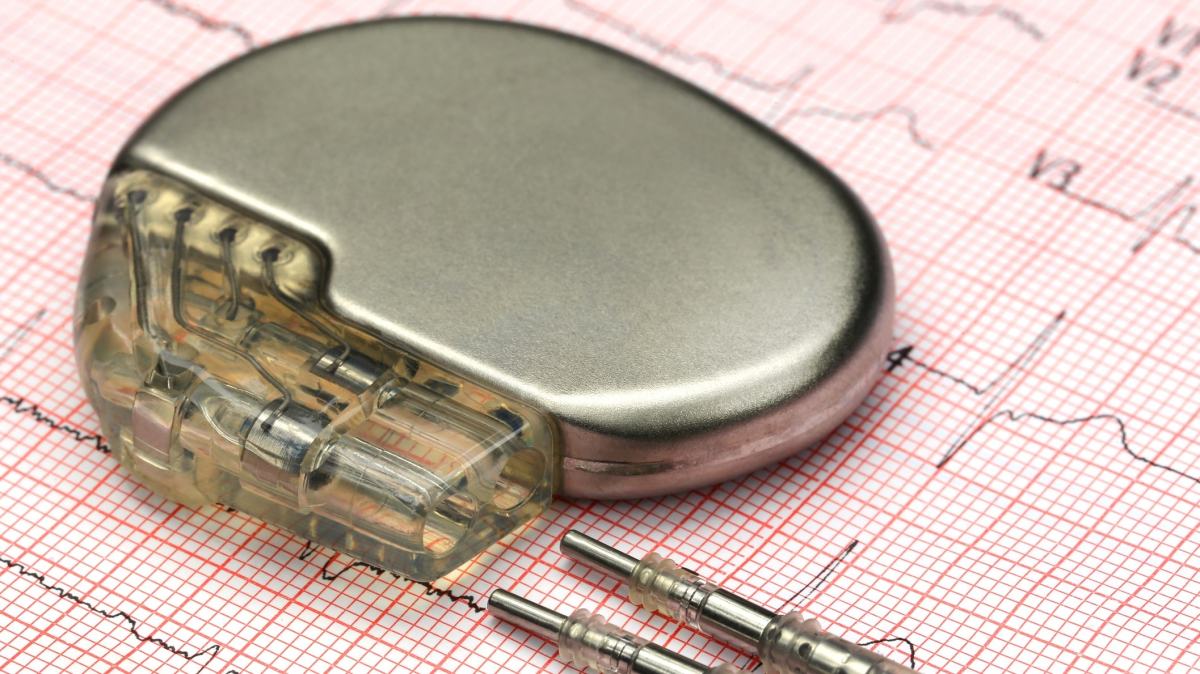
Pacemakers from Abbott Laboratories can be hacked due to three significant vulnerabilities, the Department of Homeland Security’s CERT team announced on Tuesday, prompting the manufacturers to issue updates to address security and dangerous battery problems.
It’s a complex and difficult flaw to exploit, according to CERT, but the danger is real. A nearby hacker can gain unauthorized access to the heart implants allowing them to issue commands, change settings and interfere with the pacemaker’s functionality. The pacemakers deliver electrical pulses to correct a slow, irregular or stopped heart. Interference could result in a target’s death. Attackers have to be within inches of the target to exploit the vulnerability via radio frequency (RF) communications.
The pacemakers impacted are the following St. Jude Medical pacemaker and CRT-P devices:
- Accent
- Anthem
- Accent MRI
- Accent ST
- Assurity
- Allure
MedSec Holdings, a third-party security research firm, identified the vulnerabilities in the devices made by Abbott Laboratories, formerly known as St. Jude Medical before a January 2017 acquisition. Abbott sued MedSec in 2016 claiming that previous vulnerabilities reports were false — before eventually fixing those vulnerabilities in early 2017. That incident was linked to an FDA probe of MedSec Holdings and short-selling firm Muddy Waters who shorted shares of St. Jude Medical and reportedly almost derailed the $25 billion acquisition by Abbott.
Fixing the issue isn’t exactly like updating your phone. The FDA tells individuals with a pacemaker to consult a doctor to see if the approved firmware update should be applied. About 465,000 people use these devices in the United States alone.
There are no known reports of patient harm related to these vulnerabilities.
“The firmware update requires an in-person patient visit with a health care provider – it cannot be done from home via Merlin.net,” the FDA explained. “The update process will take approximately 3 minutes to complete. During this time, the device will operate in backup mode (pacing at 67 beats per minute), and essential, life-sustaining features will remain available. At the completion of the update, the device will return to its pre-update settings.”
Abbott identified a distinct battery issue impacting its heart devices in 2016 that resulted in a recall of 400,000 devices and two deaths in Europe.
The new incident underlines concerns about the increasingly connected nature of medicine in the 21st century. This year’s WannaCry malware outbreak crippled hospitals around the globe. The state of healthcare cybersecurity has been bemoaned in many respects as a disaster waiting to happen and it ranks among the lowest performing industries in the country.
Abbott emphasized — and regulators agreed — that continued treatment offered sizable benefits that made the possible cyber risks worthwhile.
“The FDA reminds patients, patient caregivers, and health care providers that any medical device connected to a communications network (e.g. wi-fi, public or home Internet) may have cybersecurity vulnerabilities that could be exploited by unauthorized users,” the FDA’s blog read. “However, the increased use of wireless technology and software in medical devices can also often offer safer, more efficient, convenient, and timely health care delivery.”
“Connected devices are having a significant positive impact for patients and their health,” Robert Ford, executive vice president of Medical Devices at Abbott, said in a statement. “To further protect our patients, Abbott has developed new firmware with additional security measures that can be installed on our pacemakers.”


