Misconfiguration leaves thousands of servers vulnerable to attack, researchers find
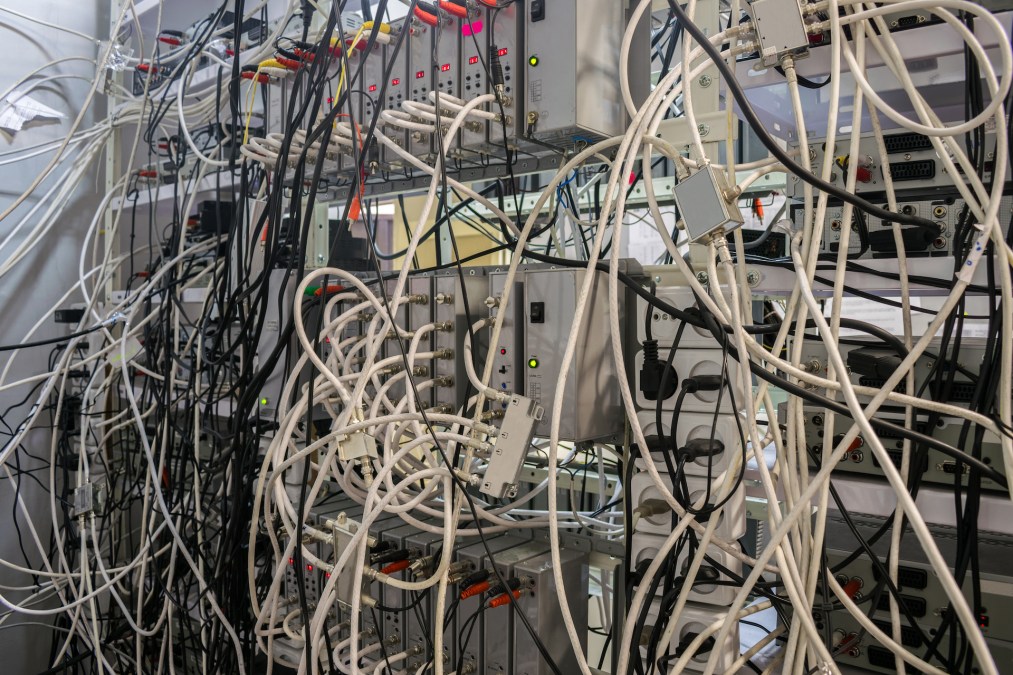
Misconfigured web servers remain a “major problem” with thousands left exposed online waiting for hackers to gain access to valuable information that’s left up for grabs, according to a recent report from the security company Censys.
The firm that indexes internet-facing devices found that more than 8,000 servers hosting sensitive information such as log-in credentials, database backups and configuration files are not property configured.
The data in the company’s their latest State of the Internet report released Wednesday is yet another troubling sign that many organizations are still not taking basic security precautions to safeguard their own data — as well as their customers’ information.
“In the past decade, some of the most significant data breaches were not caused by advanced nation-state-developed zero-day attacks,” the report noted. “Rather, many of them occurred due to human error, where a mistake led to the exposure of large amounts of data on a server without any security measures in place, such as authentication, authorization, or filtering.”
The firm found more than 18,000 comma separated value files and more than 2,000 structured query language database files — which typically hold important data such as financial documents or sensitive intellectual property — all with zero authentication requirements. While the firm did not look at the contents of those files, “their mere existence on a publicly accessible web server should be enough to raise alarms,” the firm noted.
Censys pointed to a data leak of more than 1.8 million Texas residents personal information last year and one of many examples of the long-standing issue.
Censys also found that there are thousands of end-of-life internet-facing devices with widely known vulnerabilities. Hikvision, a Chinese video surveillance company that was recently banned by the Federal Communications Commission due to national security threats, is one of the top services found with “potentially tens of thousands” of devices with a widely known vulnerability.
“The often unglamorous work of asset, vulnerability, and patch management is critical for helping reduce an organization’s attack surface. The security issues we’ve explored in this report aren’t a result of zero days or other advanced exploits, but rather misconfiguration and exposure issues that are likely a result of simple mistakes or configuration errors,” Censys noted.



