Iranian steel facilities suffer apparent cyberattacks
Three Iranian steel companies suffered apparent cyberattacks Monday, claimed a hacktivist group that previously took responsibility for a digital assault on the Iranian train system with wiper malware.
Iranian state media seemingly confirmed the attacks, writing that “part of the steel information technology systems of the country was attacked by foreign enemies.”
A hacktivist group calling itself “Gonjeshke Darande” claimed responsibility for the attacks in messages posted to its Telegram channel and on Twitter. The group posted screenshots purportedly showing the inside of one of the steel facilities and what appears to be an industrial control dashboard.
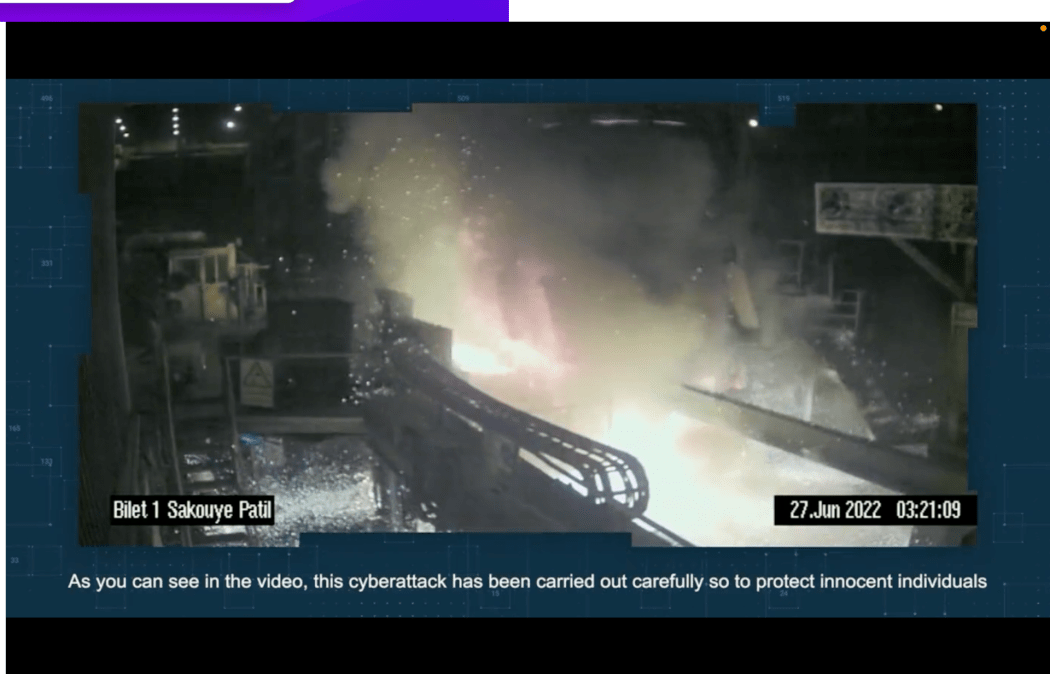
A video shared by the group, with a date stamp of June 27, appears to show equipment being damaged and a subsequent fire, with firefighters rushing in to extinguish the flames. Operations at one of the companies, Khuzestan Steel — reportedly one of Iran’s largest — were suspended as a result of the attack, the BBC World Service’s Persian portal reported Monday. The CEO of that company told an Iranian news source that “the attack failed and no damage was done to the production line,” according to a Google translation.
“These companies are subject to international sanctions and continue their operations despite the restrictions,” the group wrote. “These cyberattacks, being carried out carefully so to protect innocent individuals, are in response to the aggression of the Islamic Republic.”
The same group claimed responsibility for the July 2021 wiper malware attacks on the Iranian railway system that reportedly caused widespread train delays and disruptions. That attack included a message displayed on train schedule screens directing angry passengers to contact the Iranian Supreme Leader’s office with complaints. A subsequent attack on the Iranian state service that subsidizes gasoline purchases in October 2021 displayed a similar message on gas pumps, causing some observers to say the attacks were aimed at destabilizing the Iranian government as part of a cyber tit-for-tat between Israel and Iran.
Researchers with cybersecurity firm SentinelOne’s SentinelLabs dubbed the malware that hit the train system “MeteorExpress.” SentinelLabs Principle Threat Researcher Juan Andrés Guerrero-Saade, who wrote the MeteorExpress report, tweeted Monday that the group associated with MeteorExpress has “used a variety of false fronts,” including Indra, Gonjeshke Darande, Predatory Sparrow and possibly Edalat Ali, which in February 2022 posted closed circuit video and documents from an Iranian prison that held political prisoners.
The Telegram account associated with Edalat Ali posted a forwarded message from the Gonjeshke Darande Telegram channel claiming responsibility for the attack Monday.
Representatives of the group had previously claimed to be Iranians living and working inside Iran trying to expose inhumane treatment of prisoners.
“While people debate the role of cyber in a hot conflict like the war in Ukraine, there are wellsprings of novel cyber activity in other regions going entirely unexamined,” Guerrero-Saade told CyberScoop Monday. He added that the group’s approach in this case — claiming to avoid collateral damage on civilians and only target sanctioned companies — was interesting.
“There’s something novel happening here that warrants further scrutiny,” he said.
Itay Cohen, the head of cyber research for American-Israeli firm Check Point, said in an email that the hacks “joins a flood of attacks conducted by groups portraying themselves as Hacktivists against the regime.” Check Point has analyzed several similar incidents, including ones targeting an Iranian national media corporation in January 2022 and the July 2021 railway hack.
“The number of attacks, their success and their quality can suggest that they were conducted by an advanced attacker or attackers, perhaps a nation-state with an interest to sabotage Iran’s critical infrastructure,” Cohen said, “as well as seed panic among the Iranian public and officials.”
John Hultquist, the vice president of intelligence for Mandiant, said in a statement Monday that the firm is “working to validate the claims” of a physically destructive attack, but noted that the screenshots and evidence posted are not necessarily indicative of an actual intrusion into the operational technology of the facility.
But, in “some respects, it doesn’t really matter if this was a cyber attack or not,” he added. “The evidence that was provided by the alleged attacker may be sufficient to convince many that a cyber attack occurred, serving the attacker‘s purposes.”
Update 6/28/22: to include comments from the CEO of Khuzestan Steel Company.



