DEF CON Voting Village report explores vulnerabilities in ballot-marking devices, calls for paper-based audits
After finding security weaknesses in two ballot-marking devices at this year’s DEF CON Voting Village, researchers are calling for “more comprehensive studies” of equipment that is increasingly a part of the voter experience.
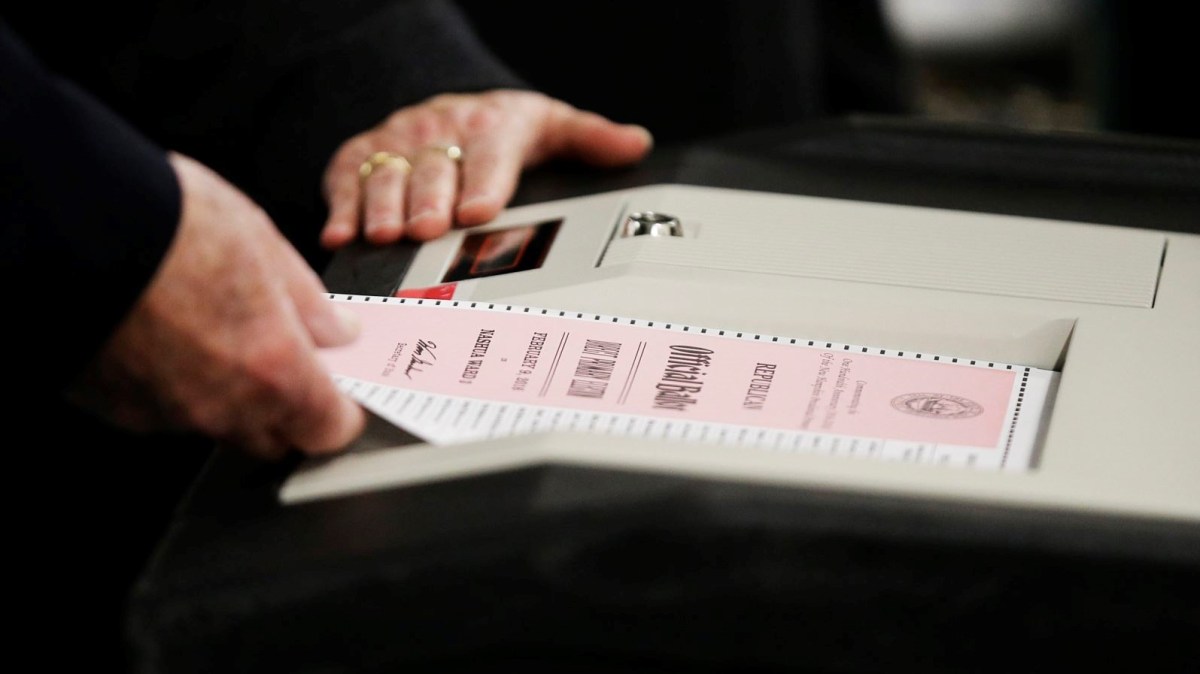
The findings come as states consider the security advantages of election systems that create a paper trail. Ballot-marking devices, or BMDs for short, allow voters to mark their choices on a screen and then print them out. The paper ballots are then counted by hand or scanned by a separate machine.
“The security implications of ballot marking devices should be further studied,” researchers said in the 2019 Voting Village report, which sums up more than two days of hacking and tinkering at a Las Vegas casino in August. “Current and proposed next-generation ballot marking devices have not been designed with security considerations in mind,” they argued.
The researchers say that data stored by the two BMDs they studied could be tampered with or that the devices could be disrupted via a denial-of-service attack. One “hybrid” ballot-scanning and marking device had an internal network connecting the two, meaning an attacker who breached one could compromise the other. The researchers acknowledged that their sample size is very small, and asked the cybersecurity community to do more to examine the equipment.
Joseph Lorenzo Hall, chief technologist of the Center for Democracy & Technology, said that BMDs, if designed properly and securely, can improve the voter experience, and that a number of academics are studying the issue.
“It will be very important to study carefully the results of these investigations to understand how we can ensure that machine-marking translated into verification of the paper, and what design patterns are necessary to encourage most voters to do so,” said Hall, who praised the DEF CON report as “in general very good” and a “great read-out” of lessons learned from the hacking conference.
The findings are one of multiple security challenges highlighted in the Voting Village report, an annual exercise in galvanizing public interest in making election systems more secure. The researchers also said they were able to remotely manipulate the memory card of a popular optical ballot scanner when it is connected to the network. And they found weaknesses in passwords used by some of the voting equipment, with a supervisory password stored in plaintext for one electronic pollbook.
The report comes as the entire election ecosystem, from federal, state and local officials to vendors, looks to make security improvements for the 2020 presidential election, which U.S. officials warn will again draw foreign interference attempts.
The organizers independently acquired voting equipment from all three of the country’s major vendors: Election Systems & Software, Dominion Voting Systems and Hart InterCivic. The vendors, which some researchers have criticized as slow to embrace ethical hacking, still did not formally participate in the village this year. They have, however, begun developing a coordinated vulnerability disclosure program.
The village organizers also issued a plea for paper-based audits that election-security experts have long called for but the country still lacks in some places.
“Post-election audits are the only known way to secure elections conducted with imperfect hardware and software [as all modern computer-based hardware ultimately is],” the report says.
According to the National Conference of State Legislatures, some 33 states plus the District of Columbia conduct a post-election audit that involves comparing some percentage of voting machine records with paper ballots.



