Surveillance campaign against Libyans uses fake Johns Hopkins COVID-19-tracking map
It’s not just opportunistic, financially-motivated criminals who are seizing on the novel coronavirus pandemic to conduct cyberattacks. Operators of spyware are also exploiting the health crisis to boost their surveillance efforts.
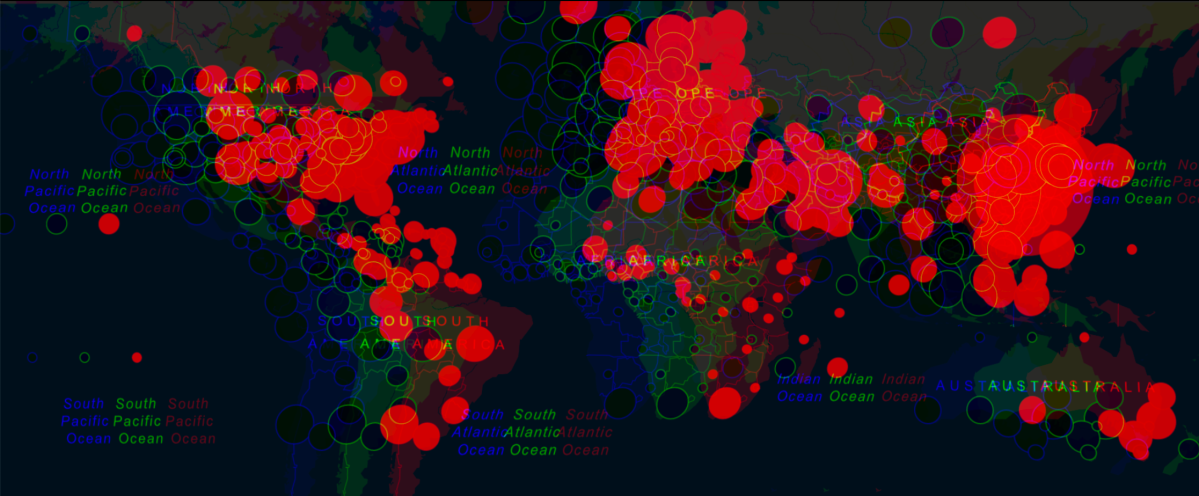
Mobile security firm Lookout has traced a malicious Android application to what it says is a long-running campaign to spy on people in Libya. The spyware masquerades as the popular map produced by Johns Hopkins University that tracks the spread of COVID-19, the disease caused by the novel coronavirus.
The software, called SpyMax, allows the operator to exfiltrate call and text logs, and remotely activate microphones and cameras.
“In terms of other mobile malware that has been seen taking advantage of COVID-19 fears, this is the most invasive I’ve seen,” Kristin Del Rosso, Lookout’s security research engineer told CyberScoop.
The broader spying campaign has gone on for nearly a year, but its evolution shows how surveillance-minded hackers can exploit the COVID-19 crisis.
It started with applications targeting specific Libyan phone numbers, and then malicious code related to media players. “Only recently, in the midst of this pandemic, did we see two samples pertaining to COVID-19,” Del Rosso said. The latest sample was signed in mid-March. The malicious apps were never in the Google Play store, Lookout said.
The discovery shows how hacking groups with different motives will exploit the pandemic differently. There has been a surge in COVID-19-themed phishing activity from various actors that have prompted warnings from the World Health Organization and U.S. authorities.
A “new short-term actor” will likely look to defraud people through ransomware and desktop phishing, Del Rosso said. But a “long-term actor with surveillance goals” – like the one active in Libya — will have plenty of infrastructure in place that has been effective in past spying campaigns, she added.
“An existing surveillance actor realizes it takes time, and often multiple attempts, to create the right malware that looks interesting enough for your target to download,” Del Rosso added. The COVID-19 outbreak is a great opportunity to leverage that malware.
More than nine years after the fall of former dictator Moammar Gadhafi, Libya remains in turmoil, as warring factions continue to vie for power.
Lookout doesn’t know how many mobile phones have been infected by the malware. There has been no indication that the hacking effort is state-sponsored, the firm said. Whoever is behind the spying campaign has been using IP addresses apparently tied to a Libyan telecommunications firm.
The surveillance tools are available on the cheap, part of a broader family of spyware that can be tailored to one’s needs. Such spyware will remain a convenient tool for anyone looking to track an adversary.



