The key to protecting the midterms is resilience for election systems, experts say

With less than three weeks until the midterm elections, a lot of work has gone into preparing for the threat of election interference. But experts speaking at the CyberTalks conference on Thursday acknowledged that disaster could still strike, and that the officials who run U.S. elections have to be armed with proper resources and resilient systems.
“We’re not seeing activity right now relating to direct election hacking. We’re not seeing anything right now along the lines of 2016, and that frankly makes me a little nervous,” said Homeland Security Undersecretary Chris Krebs. “So we’re working aggressively with our partners, the state and local [officials] to work through what an adversary could do with a two-and-a-half-week lead-up to the midterm elections.”
U.S. intelligence officials have stressed over the past two years that Russia attempted to interfere in the 2016 election. Krebs said the hope is now to avoid a “failure of intelligence” and “failure of imagination” as to how adversaries could target the midterms.
“To me the question is not ‘Will the system be breached at some point?’ Absolutely, it will,” said Robby Mook, a former campaign manager for Hillary Clinton’s 2016 presidential campaign. “The question is: Do we have good systems in place such that every vote that is cast is eventually counted properly?”
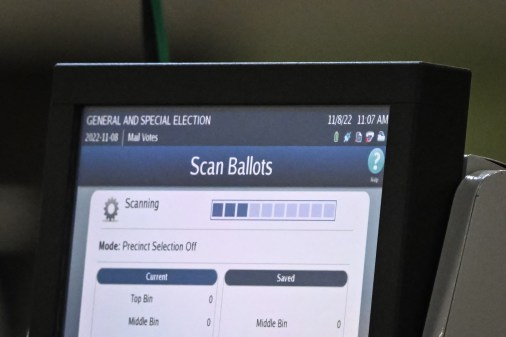
Experts have been pushing states and localities to ditch paperless voting machines amid the ongoing election security concerns. Without a paper record of each vote, experts warn there could be no way to recover from a potential hack on a voting machine.
Mook said that this problem is largely the result of a 2002 law that gave states funding to buy new voting technology for the sake of accessibility and technological advancement. Earlier this year, Congress used that law — the Help America Vote Act (HAVA) — to provide states with a $380 million fund to improve their election systems. Much of those funds have gone to security upgrades and plans to replace paperless machines.
“We are living today with the the Help America Vote Act and some of the fallout of that. After the 2000 election, there was a rush to buy machines, and I don’t know that we thought carefully enough about what we really need and what’s the most secure thing,” Mook said. “I think investing more in research can help guide these decision-makers and what system they purchased.”
Matt Masterson, a senior cybersecurity adviser at DHS who spoke on a panel with Mook at CyberTalks, agreed that election technology upgrades need more forethought on security than they had in the early 2000s.
“We had the funds, which I think was an incredible investment from Congress, but we didn’t have the certification regime in place and the standards for the money being spent,” Masterson said. “That’s one of these huge lessons learned — this not just for addressing and dumping money, but an ongoing investment to secure what is critical infrastructure: our election systems.”
Maybe some good came of 2016?
Despite the national alarm that the issue of election interference has caused since 2016, officials pointed to some silver linings. Namely, they said it brought increased collaboration across government and industry and an elevated sense of importance for cybersecurity as a whole.
“We were in a position where we had intelligence, we were trying to stitch together a response, but we didn’t have the relationships to effectively respond and defend our election infrastructure,” Krebs said of the state of election security in 2016. He and his peers argue that things are different now.
“One of the really positive outcomes of 2016 is the amount of engagement from folks that we’ve never had in the elections community before,” Masterson said, pointing to the Harvard Belfer Center’s Defending Digital Democracy Project, where Mook sits as a senior fellow, as an example. The center held a tabletop exercise with election cyberattack scenarios in which almost every state participated.
Additionally, several technology companies have offered free products and services to help election offices secure their systems. DHS has also been engaging with states to provide training, cyber-hygiene scans, security sensors and other resources.
“We are so much farther ahead than where we were. Everyone was surprised by what happened in 2016,” Mook said.
Krebs argued that the election interference scare also brought more people to see cybersecurity as a national security issue.
“It finally dawned on the American people that cybersecurity was not just intellectual property theft. It was not just cybercrime,” Krebs said. “It was a vector. It was a threat that could directly undermine our way of life in our constitutional republic. That was unsettling.”