Atos, IT provider for Winter Olympics, hacked months before Opening Ceremony cyberattack

Hackers armed with destructive malware appear to have compromised the main IT service provider for the Winter Olympic Games months before last week’s highly publicized cyberattack.
Publicly available evidence analyzed by experts and reviewed by CyberScoop suggests that whoever deployed the Olympic Destroyer malware on Feb. 9 likely previously penetrated a series of computer systems around December belonging to Atos, a multinational information technology service provider that is hosting the cloud infrastructure for the Pyeongchang games.
The evidence was recently posted to the VirusTotal repository, but information associated with the malware samples carries indications that the hackers were inside Atos systems since at least December. Some of the earliest samples were uploaded by unnamed VirusTotal users geographically located in France, where Atos is headquartered, and Romania, where some members of Atos’ security team work.
On Feb. 9, the official Winter Olympics website went down for several hours, causing a disruption to ticket sales and downloads during the opening ceremony. Localized Wi-Fi networks surrounding the games in South Korea also reportedly became temporarily unavailable in the preceding hours.
Olympics officials confirmed Feb. 11 that a cyberattack had hit their systems, but provided few details about the incident. One day later, security researchers with Cisco’s Talos unit said they had identified wiper malware potentially related to the disruption. The malware is designed to destroy data and cause mass computer failures.
The information reviewed by CyberScoop supports assertions by Talos researchers that whoever was behind Olympic Destroyer likely first conducted an expansive cyber-espionage operation against the Olympics before launching the attacks. The malware required a bank of authentic login credentials to actual accounts of Olympics staff in order to quickly propagate and spread a destructive payload, which deletes files, like shadow backups, boot configuration data (BCD) and event logs on infected machines.
It remains unclear how hackers were able to steal so much information from Olympics employees, but penetrating a key supply chain IT vendor may have afforded them an opportunity to conduct valuable reconnaissance. Targeting a supply chain vendor that’s connected to a well-guarded organization in order to penetrate the latter is a common tactic used by both nation state and criminal hackers.
A spokesperson with Atos confirmed to CyberScoop that there’s an ongoing investigation into a possible breach at Atos related to the Olympics incident.
“Following technical incidents during the Olympic Games Pyeongchang 2018 opening ceremony, a thorough investigation is being conducted,” the spokesperson said in an email. “Together with our partner McAfee Advanced Threat Research, we can confirm that the cyberattack, which caused no critical disruption of the Olympic Games, used hardcoded credentials embedded in a malware. The credentials embedded in the malware do not indicate the origin of the attack. No competitions were ever affected and the team is continuing to work to ensure that the Olympic Games are running smoothly. At this moment in time, we are coordinating with our partners and the appropriate authorities as investigations continue.”
Atos describes itself as the “Worldwide IT Partner of the International Olympic Committee.”
“For Pyeongchang 2018 Winter Olympic Games, Atos will host their OMS/ ODS * critical applications in its secured Canopy Cloud. Test and Support will be provided remotely via the CTOC (Central Technology Operations Center) in Barcelona and the ITL (Information Testing Lab) in Madrid,” the company’s website reads.
Although it’s not clear whether the hackers used their apparent intrusion into Atos to affect the Olympics, evidence of such a compromise is nonetheless noteworthy, as it further illustrates the risks posed to relying on external services to store data and share internet applications in the cloud.
Cybersecurity professionals often upload evidence of cyberattacks that they’re responding to on VirusTotal. But by doing so, the evidence usually becomes publicly available and with the right technical expertise, can be easily discovered. Within these types of samples, other details beyond the malware code can sometimes be found — including, for example, information about the victim organization, like stolen usernames, passwords, private email addresses, confidential internal domain names and other details about network configuration. The evidence reviewed by CyberScoop contains a trove of such information apparently belonging to various employees of Atos.
The Atos-related information on VirusTotal was attached to multiple Olympic Destroyer malware samples. The connection suggests the hackers had penetrated the IT provider in recent months. The stolen data, some of which includes Atos employee usernames and passwords, is viewable if the malware samples are broken down and the “strings” are further analyzed. The original research revealing Olympic Destroyer published on Monday does not mention the possibility of a roundabout third party hack.
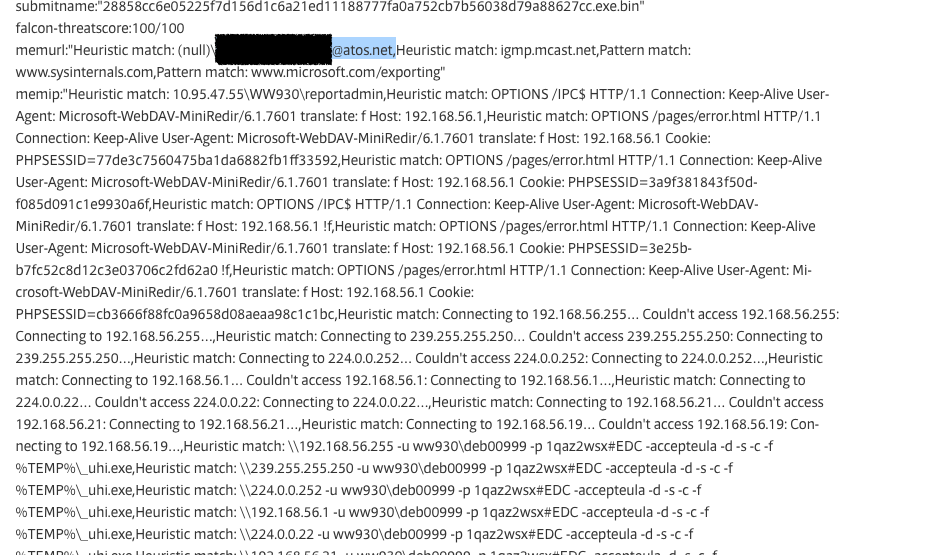
Example of string contained within one Olympic Destroyer malware sample
Cybersecurity experts say the fact that some Olympics Destroyer malware samples are embedded with Atos employee credentials shows that the IT provider was likely compromised by the same hackers that ultimately hit the Winter Olympics.
“This looks like a classic, cut-and-dry supply chain attack,” said Blake Darche, CSO of Silicon Valley-based cybersecurity firm Area 1 Security. “This is exactly who they would target if they were trying to get to the Olympics’ systems.”
Olympic Destroyer is unique in many ways. The malware’s authors engineered it so that it act like a computer worm; automatically scanning for and then stealing user credentials before then carrying them to other systems for login attempts. The design allows for the virus to effectively spread very quickly within a confined, already compromised environment, to deploy a malicious payload capable of destroying data. In a scenario like the Olympics, the mass destruction of data could cause significant disruptions to the games.